Welcome to Software Development on Codidact!
Will you help us build our independent community of developers helping developers? We're small and trying to grow. We welcome questions about all aspects of software development, from design to code to QA and more. Got questions? Got answers? Got code you'd like someone to review? Please join us.
Post History
Disclaimer: I am not a security expert nor a security professional. There is, of course, a relevant XKCD comic for this: The entropy numbers appear to be accurate based on this security.stackex...
#2: Post edited
- Disclaimer: I am not a security expert nor a security professional.
- There is, of course, a relevant [XKCD comic](https://xkcd.com/936/) for this:
- 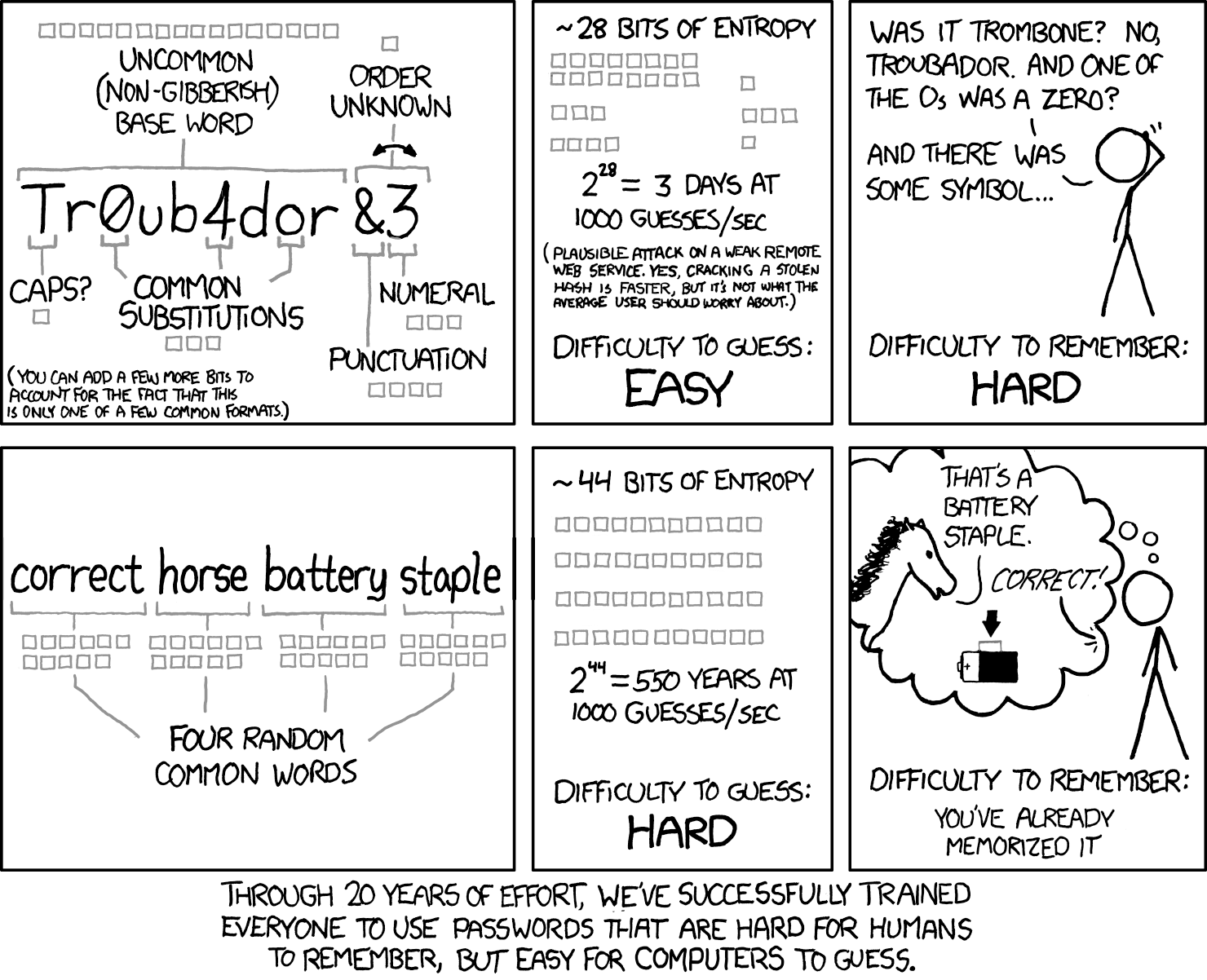
The entropy numbers appear to be accurate based on [this security.stackexchange](https://security.stackexchange.com/questions/6095/xkcd-936-short-complex-password-or-long-dictionary-passphrase) post. It actually assumes a dictionary attack, which involves checking for common words in passwords and is sometimes used to discredit the "commonhorsebatterystaple" method of password generation. However, when password checkers are looking at password strength, they usually are comparing passwords of *equal lengths*. An 8 character password with only alphabetic characters will be weaker than an 8 character password with digits, special symbols, *and* alphabetic characters. If you assume that people will use the shortest password they can get away with, then forcing them to include more variety makes sense. It also allows the site to use less database storage space while forcing better passwords than just 8 alphabetic characters.- In my personal experience, security professionals assume people will use some kind of password storage program. They don't seem to consider the difficulty of remembering the sheer number of passwords required for various necessary accounts. None of the various security seminars I have participated in for work offered any solutions. Password requirements are based on site security *for that site alone*; they don't take into account how users are supposed to handle 50 sites with difficult to remember passwords.
- To answer your question about attacks per second: [attackers aren't necessarily trying to attack over the internet](https://en.m.wikipedia.org/wiki/Password_cracking). They will use copies of databases full of hashed passwords and run hundreds of attacks per second on them. Once they have a plaintext password, they can try that on other sites such as banks (people reuse passwords enough for this to be worth it). So the password strength really can matter, especially if you reuse passwords.
- Disclaimer: I am not a security expert nor a security professional.
- There is, of course, a relevant [XKCD comic](https://xkcd.com/936/) for this:
- 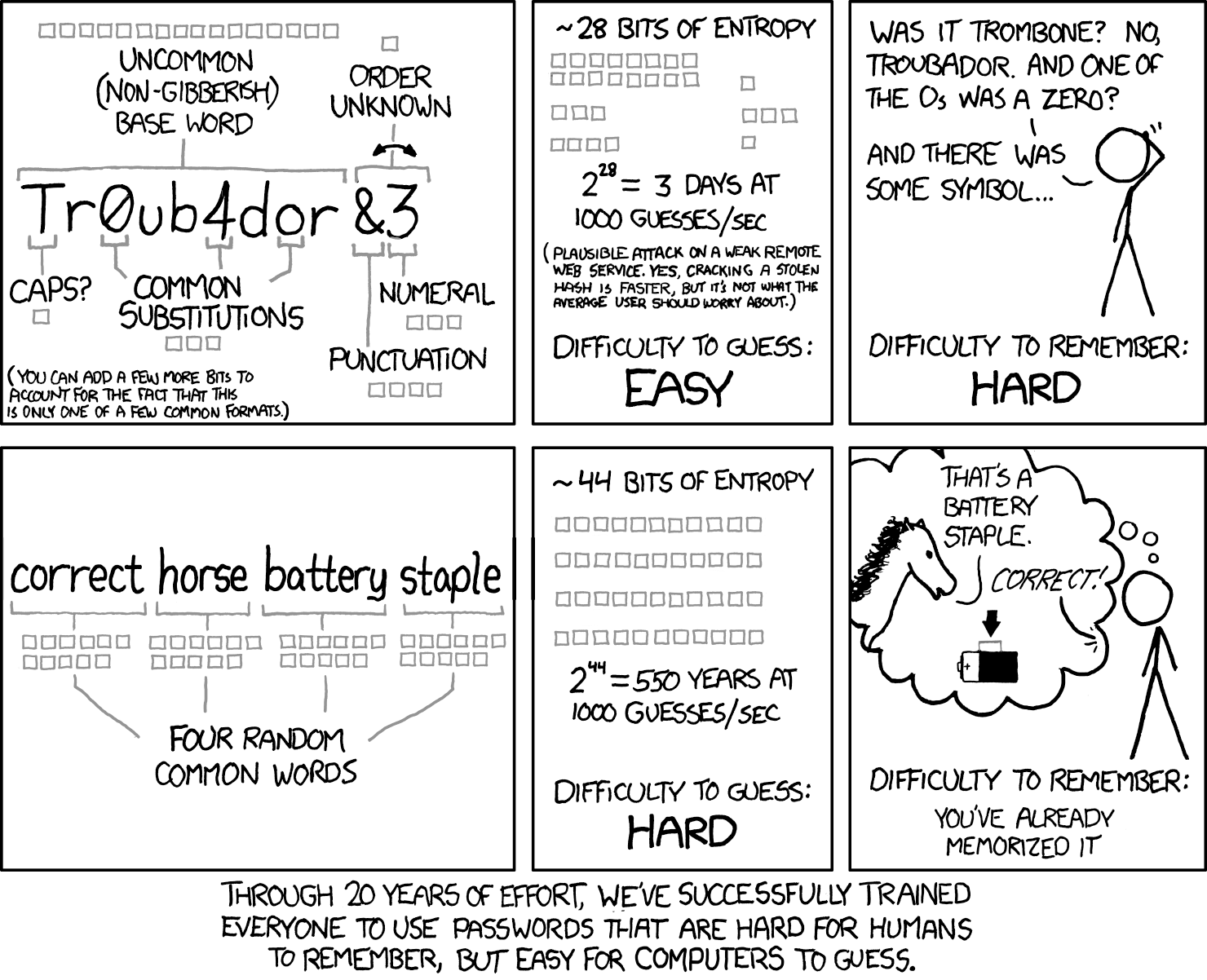
- The entropy numbers appear to be accurate based on [this security.stackexchange](https://security.stackexchange.com/questions/6095/xkcd-936-short-complex-password-or-long-dictionary-passphrase) post. It actually assumes a dictionary attack, which involves checking for common words in passwords and is sometimes used to discredit the "correcthorsebatterystaple" method of password generation. However, when password checkers are looking at password strength, they usually are comparing passwords of *equal lengths*. An 8 character password with only alphabetic characters will be weaker than an 8 character password with digits, special symbols, *and* alphabetic characters. If you assume that people will use the shortest password they can get away with, then forcing them to include more variety makes sense. It also allows the site to use less database storage space while forcing better passwords than just 8 alphabetic characters.
- In my personal experience, security professionals assume people will use some kind of password storage program. They don't seem to consider the difficulty of remembering the sheer number of passwords required for various necessary accounts. None of the various security seminars I have participated in for work offered any solutions. Password requirements are based on site security *for that site alone*; they don't take into account how users are supposed to handle 50 sites with difficult to remember passwords.
- To answer your question about attacks per second: [attackers aren't necessarily trying to attack over the internet](https://en.m.wikipedia.org/wiki/Password_cracking). They will use copies of databases full of hashed passwords and run hundreds of attacks per second on them. Once they have a plaintext password, they can try that on other sites such as banks (people reuse passwords enough for this to be worth it). So the password strength really can matter, especially if you reuse passwords.
#1: Initial revision
Disclaimer: I am not a security expert nor a security professional. There is, of course, a relevant [XKCD comic](https://xkcd.com/936/) for this: 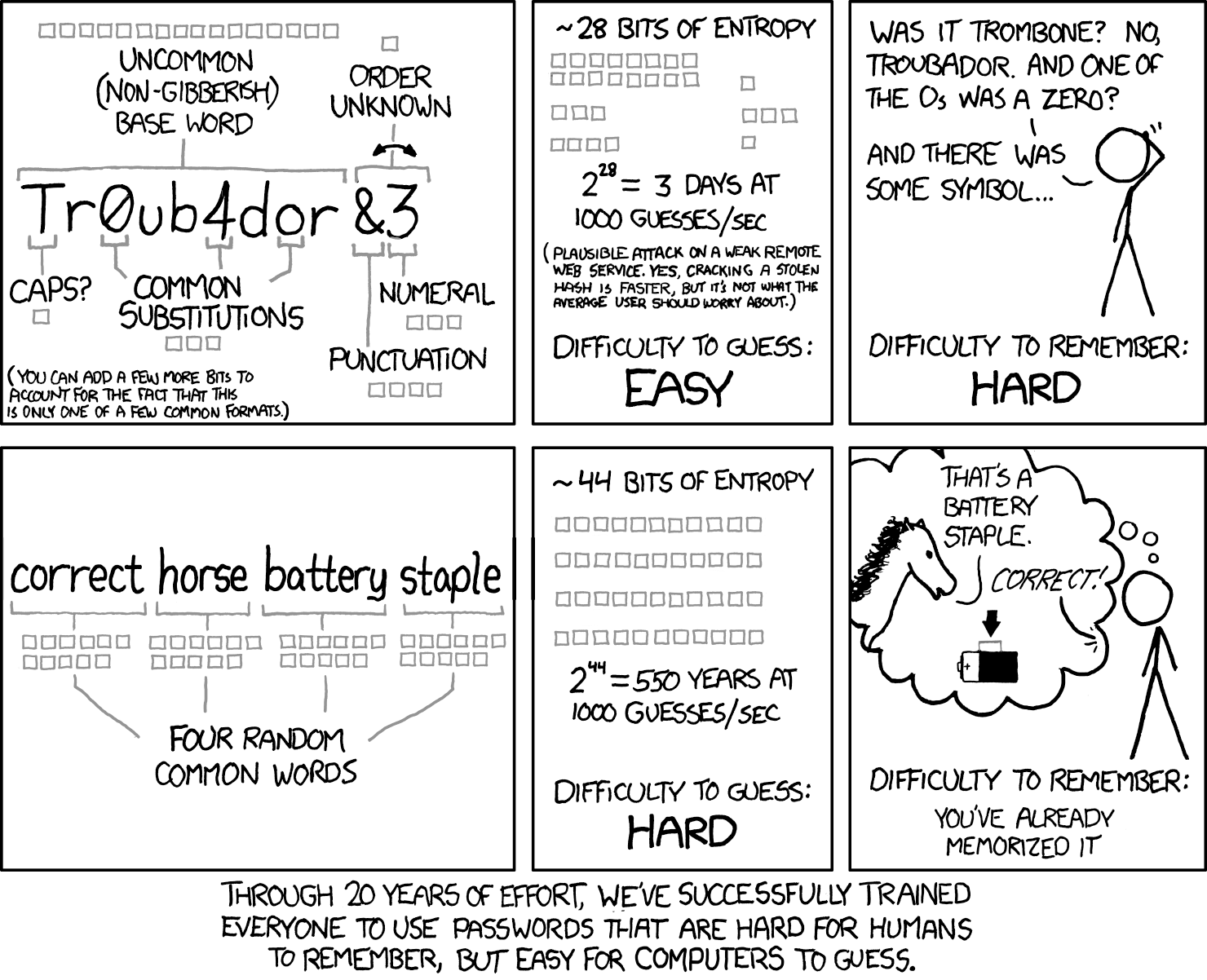 The entropy numbers appear to be accurate based on [this security.stackexchange](https://security.stackexchange.com/questions/6095/xkcd-936-short-complex-password-or-long-dictionary-passphrase) post. It actually assumes a dictionary attack, which involves checking for common words in passwords and is sometimes used to discredit the "commonhorsebatterystaple" method of password generation. However, when password checkers are looking at password strength, they usually are comparing passwords of *equal lengths*. An 8 character password with only alphabetic characters will be weaker than an 8 character password with digits, special symbols, *and* alphabetic characters. If you assume that people will use the shortest password they can get away with, then forcing them to include more variety makes sense. It also allows the site to use less database storage space while forcing better passwords than just 8 alphabetic characters. In my personal experience, security professionals assume people will use some kind of password storage program. They don't seem to consider the difficulty of remembering the sheer number of passwords required for various necessary accounts. None of the various security seminars I have participated in for work offered any solutions. Password requirements are based on site security *for that site alone*; they don't take into account how users are supposed to handle 50 sites with difficult to remember passwords. To answer your question about attacks per second: [attackers aren't necessarily trying to attack over the internet](https://en.m.wikipedia.org/wiki/Password_cracking). They will use copies of databases full of hashed passwords and run hundreds of attacks per second on them. Once they have a plaintext password, they can try that on other sites such as banks (people reuse passwords enough for this to be worth it). So the password strength really can matter, especially if you reuse passwords.


















